April 22, 2026
From performance to risk: why cybersecurity is becoming a decisive factor in European solar projects
Share my #SolaXStory
For a long time, solar projects in Europe were judged mainly on performance, efficiency, and cost.
That is beginning to change.
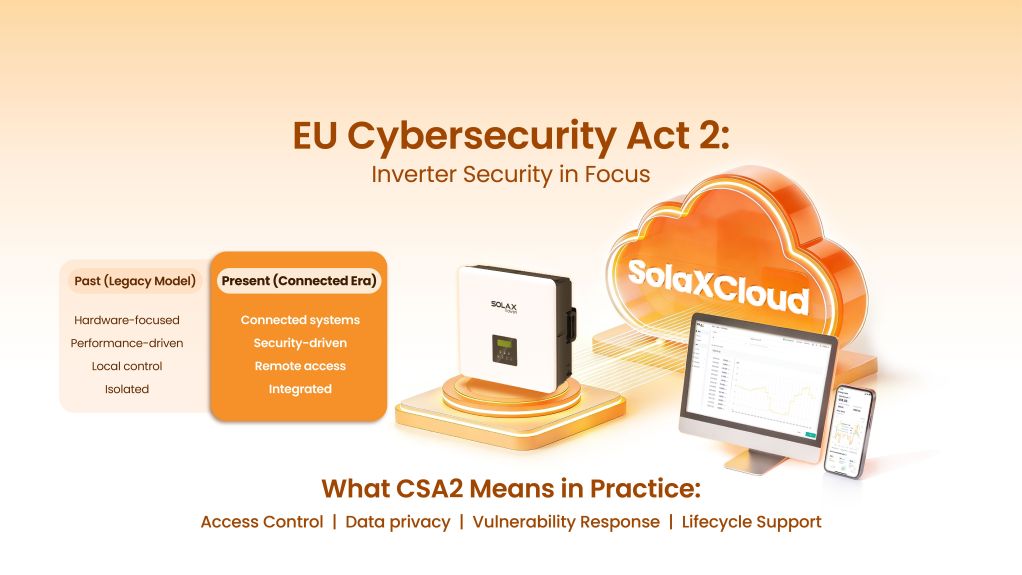
As systems become more connected, cybersecurity is moving out of the background. It is starting to influence how projects are evaluated — not just from a technical standpoint, but in terms of risk, compliance, and supplier selection.

Solar installations are no longer standalone assets. Inverters connect to cloud platforms, batteries, monitoring systems, and energy management tools. They exchange operational data, receive updates, and often allow some level of remote access.
In this context, questions about access, control, and data handling are no longer secondary. They are becoming part of the core discussion.
A regulatory push, but not from one direction
The shift in Europe is not driven by a single regulation. It is the result of several frameworks evolving at the same time.
At the organizational level, the NIS2 Directive raises expectations around risk management, incident reporting, and operational continuity in sectors such as energy. At the product level, the Cyber Resilience Act (CRA) introduces requirements for secure design, vulnerability handling, and long-term updates.
At the same time, discussions around the Cybersecurity Act are expanding the focus to include supply chain transparency and ICT trust.
The overall direction is becoming clearer, but implementation still differs across member states and use cases. What is consistent is the expectation that connected energy systems need to be more transparent and more resilient over time.
Why inverters are drawing more attention
Inverters are increasingly at the centre of this discussion.
Their role goes well beyond power conversion. In many systems, they are involved in monitoring, configuration, software updates, and communication with external platforms. That means they play a direct role in how systems are controlled and maintained in practice.
For that reason, cybersecurity due diligence often focuses on inverters early in the evaluation process.
The questions tend to be straightforward:
Who can access the system remotely?
What can be changed from a distance?
Can remote access be limited or switched off?
Where is operational data stored and processed?
How are vulnerabilities identified and addressed?
How long will updates be provided?
These are not abstract concerns. They shape how systems are managed once they are in operation.
A shift in procurement priorities
Procurement discussions are starting to reflect this.
Performance and pricing still matter, but they are no longer the only points of comparison. Buyers are paying more attention to how systems behave over time — particularly when remote access, updates, and data flows are involved.
Certifications are still relevant, but on their own they are rarely enough. What matters more is whether manufacturers can explain, in practical terms, how their systems are operated, maintained, and secured over their lifetime.
This shift is not just theoretical. It is already starting to show up in how projects are assessed.
What this looks like in practice
There are early signs of this change at project level.
Under the EU's NIS2 Directive, photovoltaic assets are increasingly treated as part of critical infrastructure. This means operators are expected to manage cybersecurity risks across both IT and operational systems, including inverters and monitoring platforms.
At the same time, connected devices — such as inverters, storage systems, and energy management platforms — are expected to demonstrate secure operation from the planning stage, rather than only at the point of compliance.
These expectations are beginning to appear in procurement processes. In recent utility-scale and C&I tenders, cybersecurity-related information is being requested as part of technical due diligence. This can include remote access controls, data storage arrangements, and software update policies.
In some cases, this is already affecting how suppliers are assessed. Systems that cannot clearly explain access control or update mechanisms may face additional scrutiny, even if they meet traditional performance requirements.
This is still evolving, but the direction is clear: cybersecurity is gradually moving from a compliance topic to something that affects how projects are delivered in practice.
How manufacturers are responding
Manufacturers are responding in different ways.
Some are focusing on aligning with emerging European requirements. Others are building more structured internal processes around cybersecurity.
SolaX is one example. The company has adopted frameworks such as ISO/IEC 27001 and SOC 2, and has completed both SOC 2 Type I and Type II assessments — a combination that is still relatively uncommon in the solar sector.
It has also aligned with a number of European requirements, including GDPR and standards such as ETSI EN 303 645 and EN18031, which are increasingly referenced in discussions around connected device security.

In practice, this is reflected in areas such as remote access control, data protection, and vulnerability management, as well as in efforts to integrate security considerations into product design and day-to-day operation.
More broadly, some manufacturers are moving towards end-to-end approaches, where cybersecurity is considered across infrastructure, devices, software, and operational processes, rather than treated as a set of isolated features.
What comes next
Europe is unlikely to ease its expectations in this area.
As energy systems continue to digitalize, cybersecurity will increasingly appear in procurement decisions, supplier evaluations, and long-term asset management discussions.
For manufacturers, this means building security into products and processes from the outset. For customers, it means asking more detailed questions earlier in the project lifecycle.
For inverters, the shift is already visible. They are no longer assessed only on electrical performance, but also on how they behave as part of connected systems in real operating environments.
Table of Contents
Lastest News
Explore expert insights, practical guides, and the latest news on SolaX Power.

To the Latest Newsletter
Stay Ahead with the Latest SolaX Updates!
Subscribe
I have read and agree to Privacy Policy and User Terms